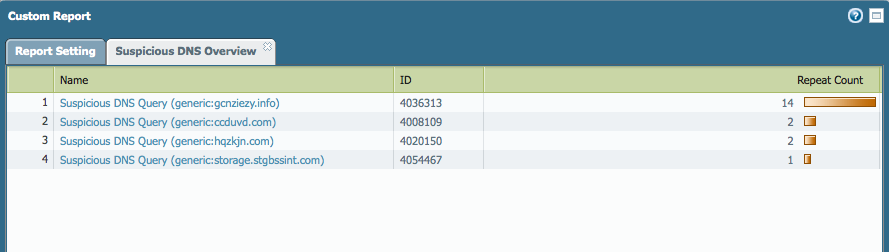
DNS queries from PAN management interface can be triggered by H... - Knowledge Base - Palo Alto Networks
DNS queries from PAN management interface can be triggered by H... - Knowledge Base - Palo Alto Networks

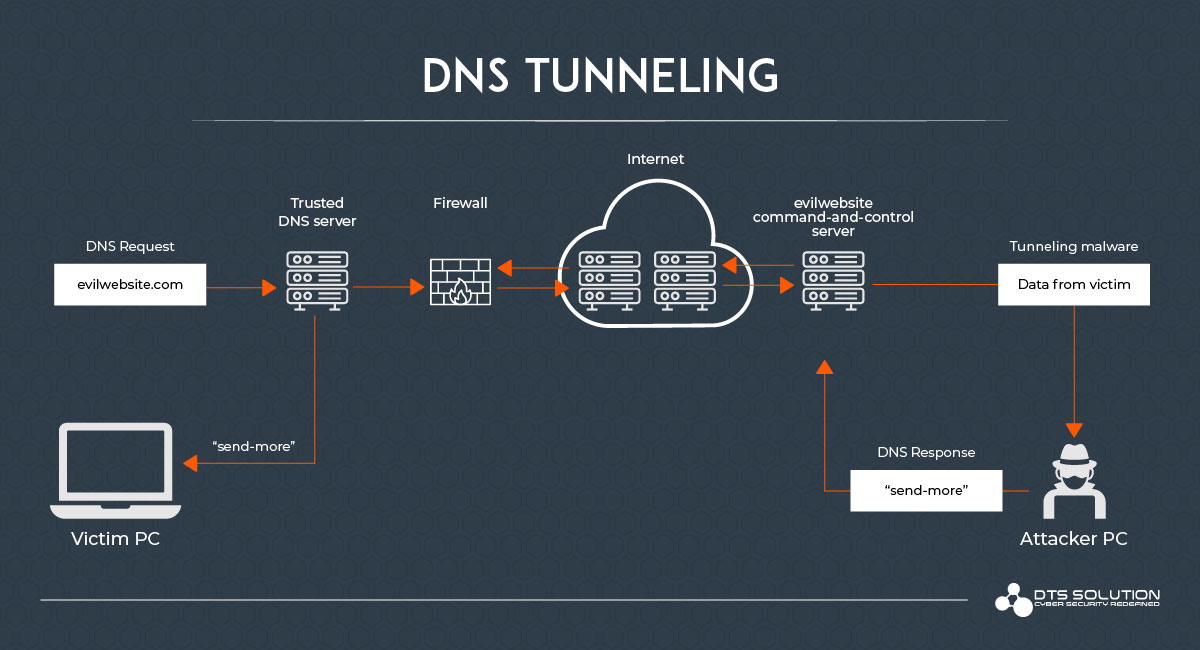
Stephan Berger on Twitter: "1/ "By using DoH, attackers can hide DNS queries from C&C domains. If SSL/TLS traffic is not being inspected using man-in-the-middle (MitM) techniques, DNS queries to the C&C






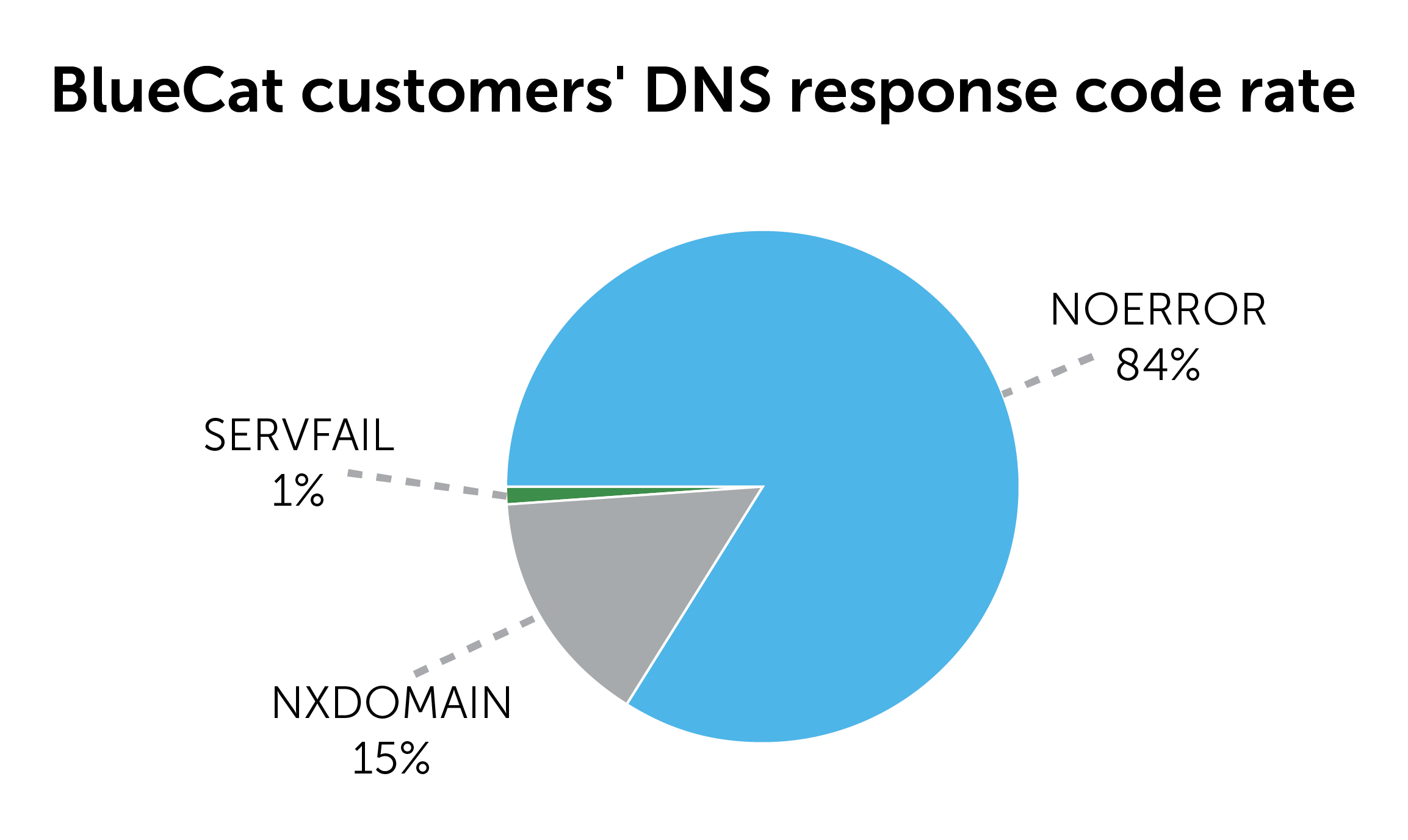
_16.44.54.png)